Protect ProxMox & TrueNAS Scale w/ CrowdStrike

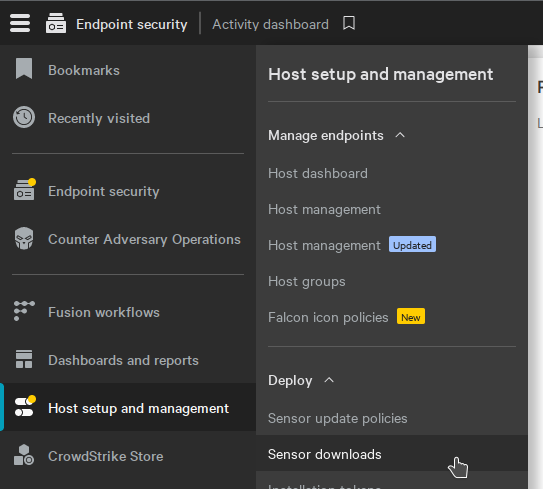
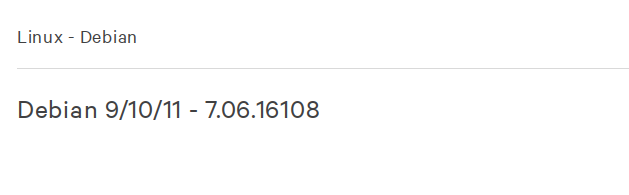
In the state of Oregon, education institutions with PACE insurance (and many others) are beginning to require not just antivirus, but antivirus with Endpoint Detection and Response (EDR). We chose to go with Crowdstrike, which, despite having the world's cringiest product names, actually provides a cheap, well-functioning base product in their Falcon antivirus. It also comes with an agent for nearly every OS you'd want it on, and the agent runs flawlessly on Proxmox (the excellent open-source hypervisor) and TrueNAS Scale (the excellent open-source NAS OS). Since both are based on Debian (the excellent stable linux distro), the install process for both is nearly identical. Since TrueNAS is pseudo-immutable (You can't install packages by default, and the rootfs is overwritten after updates) there are a few additional hoops there, but I will highlight them, don't worry!
As I've said, despite being based on Debian, TrueNAS is a pseudo-immutable system. It isn't technically designed for you to be able to install whatever packages you want. Out of the box, running apt-get will get you an error, but there is a command to enable modifications. Go ahead and run this first:
sudo /usr/local/libexec/disable-rootfs-protection
For the rest of this guide, I am going to assume you are running as the root user. To change to root, run the following:
sudo su
You now need to get that file over to your TrueNAS/ProxMox host. The easiest way to do that, especially on headless machines, is probably SCP. SCP uses SSH to transfer files securely. I didn't have to install it manually on any of our debian machines, but if need be it's as simple as:
apt update && sudo apt install scp
Open a terminal and use scp like so:
scp /[Path-To]/falcon-sensor.deb [username]@[Server-IP]:/[Destination-Path]
Which might look something like
scp /home/user/Download/falcon-sensor.deb root@10.0.10.10:/root/
Assuming SSH is set up correctly you'll be asked for a password, then your file will be dropped in /root/falcon-sensor.deb
Now pop over to the server you transferred the file to, and run the following:
First, update your package repositories:
apt update
Now install the random dependency before it screams at you:
apt install libnl-genl-3-200
Now install the actual Sensor itself:
dpkg -i /[Path-To]/falcon-sensor.deb
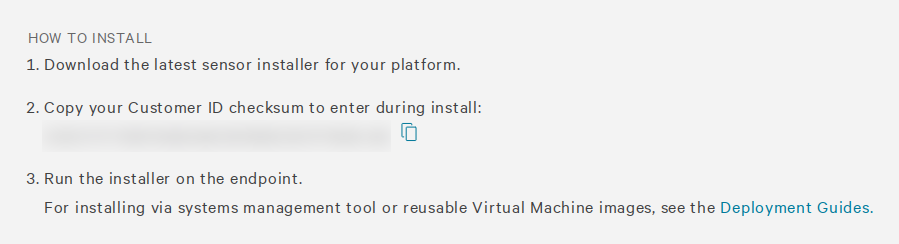
Now configure the Falcon Sensor to attach to your account:
/opt/CrowdStrike/falconctl -s --cid=YOUR-CUSTOMER-ID-GOES-HERE
Now enable and start the service:
systemctl start falcon-sensor
systemctl enable falcon-sensor
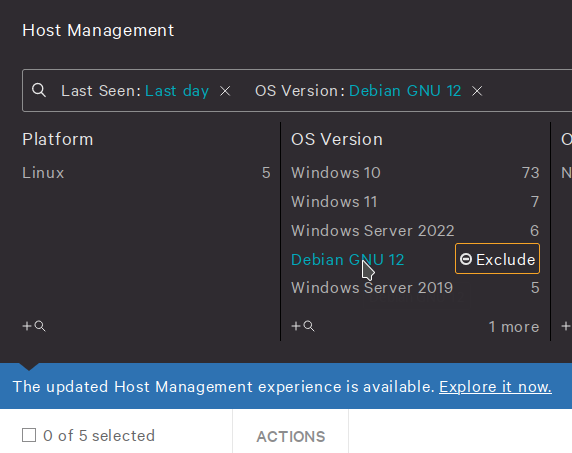
Done! Now head back to the Host Management section of the Crowdstrike Dashboard, and after a few minutes you should see Debian appear under the list of OS to filter by:

By default there are no firewall rules, as we can manage those with Proxmox's fabulous built-in firewall, but the Antivirus is set pretty aggressively.
I may dig in to optimal settings for Proxmox in another post, but for now you can tweak the policies to your hearts content! Just try not to break anything.
Additional notes on TrueNAS:
Having the Crowdstrike falcon-sensor service running prevented me from successfully upgrading TrueNAS Scale. It's a simple command to shut it off, after which you can upgrade, reboot, and it will happily start itself up again.
systemctl stop falcon-sensor
After the update, you'll need to run the command to disable rootfs protection again,
sudo /usr/local/libexec/disable-rootfs-protection
and you'll need to reinstall Crowdstrike. Luckily you'll (probably) still have the .deb file wherever you transferred it to, so you can run the command to reinstall relatively easily.
dpkg -i /[Path-To]/falcon-sensor.deb
/opt/CrowdStrike/falconctl -s --cid=YOUR-CUSTOMER-ID-GOES-HERE
systemctl start falcon-sensor
systemctl enable falcon-sensor